The security industry has spent a decade giving teams better lists. More findings. Better severity scores. Smarter prioritization. And exposure keeps growing. Not because the tools are broken. Because the operating model is.
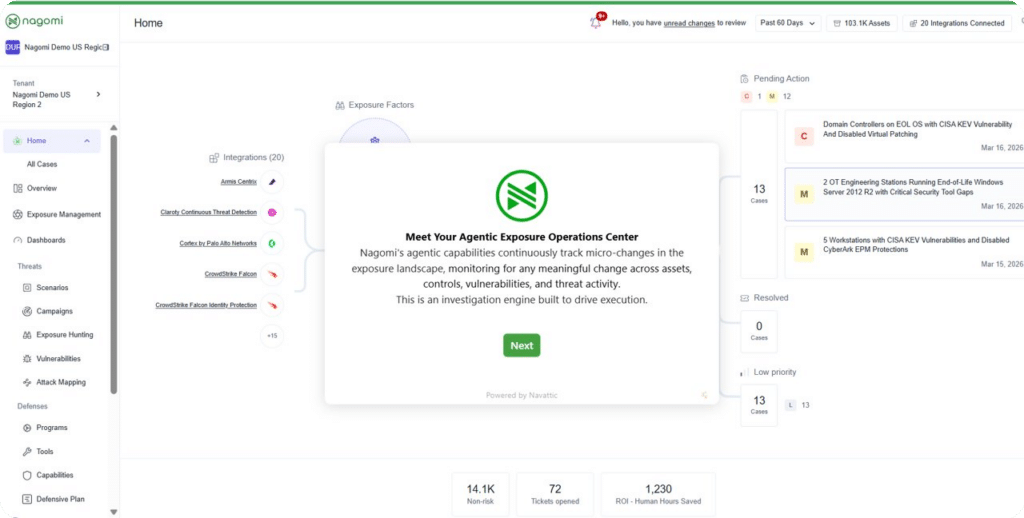
Earlier this month we introduced Agentic Exposure Ops. This is not an incremental product update. It is a fundamental change in how exposure gets eliminated.
The problem is not discovery.
You already know that.
Let me be direct. If you run a security program at any scale, you are not short on findings. Your vulnerability scanners work. Your cloud security tools work. Your EDR is deployed. Your identity platform flags misconfigurations. You might have 70 tools across your stack, and most of them are doing exactly what they were built to do: finding things.
The result is a flood of data that lands on a small team that has to manually investigate every finding, correlate it against compensating controls, determine whether real exposure exists, figure out who owns the fix, track it to completion, and then hope it stays fixed when the environment changes tomorrow.
That is not a technology problem. That is an operating model problem. And no amount of better prioritization solves it.
Traditional risk-based vulnerability management (RBVM) improved how we rank CVEs. Severity scores, exploit intelligence, asset criticality, threat feeds. All useful inputs. But RBVM still treats vulnerabilities as isolated findings. It rarely evaluates a vulnerability against the defenses and business context. A critical CVE on a non-critical managed asset with a properly configured EDR, Zero Trust, and behind a well configured WAF is a different risk profile than the same CVE on a critical and unmanaged asset, where the Zero Trust and WAF are poorly configured and completely missing the EDR. RBVM gives them the same score.
Security engineers know this. They compensate by running manual investigations. Every finding requires checking multiple consoles, cross-referencing asset data, validating control configurations, and applying judgment that takes 30 to 60 minutes per investigation. Multiply that by thousands of findings per week.
That is where the operating model breaks.
For example, our recent Illusion of Maturity report showed, fewer than 30% of assets demonstrate effective coverage across identity, endpoint, and awareness simultaneously, allowing attackers to exploit the intersections single-control metrics never reveal.
What ‘agentic’ actually means. And what it does not.
The word ‘agentic’ is everywhere right now. Every security vendor is shipping something they call an agent. Most of it is a chat interface on top of a dashboard. Ask a question. Get a summary. Figure out what to do next yourself.
That is not agentic. That is a search bar.
Nagomi’s agents are fundamentally different. They do not wait for a prompt. They do not require a human to ask the right question. They operate autonomously and continuously across your environment.
When conditions change (a new vulnerability published, a configuration drifted, a control degraded, a new privileged identity appeared, and a threat actor shifted TTPs) the agent fires. It runs a full investigation. Checks exploitability. Validates compensating controls. Assesses active threat activity. Correlates asset context. Produces a documented case with evidence, root cause, business impact, and a recommended remediation path. If the finding is clean, it documents why and moves on. No analyst touched it.
This is not AI that helps you investigate faster. This is AI that investigates for you. The analyst’s role shifts from running investigations to reviewing outcomes and approving actions.
And the system gets smarter. Early in our design partner rollout, the agent would surface task-level recommendations: patch this vulnerability, install this tool. Within weeks, it started producing root-cause guidance: figure out why that tool was not installed in the first place. Why did the configuration drift? What process gap allowed this control to degrade? That shift from task to root cause is what separates an automation script from an agent that reasons.
Not a chatbot. Not a copilot. An autonomous execution layer.
| Chatbot / Copilot | Embedded AI Assistant | Nagomi Agentic Engine | |
| Trigger | Waits for a prompt | Summarizes on request | Fires autonomously on change |
| Scope | One tool at a time | Limited to vendor data | Correlates across full stack |
| Output | Answers questions | Partial summaries | Complete investigations with evidence |
| Action | Human does the work | Human investigates | Cases with ownership and remediation |
| Verification | None | None | Continuous. Reopens on drift. |
The architecture: two layers working together
Agentic Exposure Ops is built on two layers. The first is the foundation. The second is the engine. Neither works without the other.
Context is the Foundation: The Exposure Lens
The Exposure Lens is the normalized, correlated context layer that sits across your entire security stack. It connects via read-only API integrations to your vulnerability scanners (Tenable, Rapid7, Qualys), cloud security platforms (Wiz, Palo Alto), EDR (CrowdStrike, SentinelOne), identity and access tools, email security, device management, network security, asset inventories, configuration management databases, and threat intelligence feeds and so much more.
It ingests five signal categories: vulnerabilities, misconfigurations, attack surface changes, identity gaps, and active threat intelligence. These signals are not just collected. They are correlated on a single, resolved asset view.
What does that mean in practice? A single asset might have a critical CVE from your vulnerability scanner, misconfigured network cccess solution., an identity exposure from your IAM tool, active threat group targeting from your threat intel feed, and compensating controls from your EDR and WAF. The Exposure Lens resolves all of that onto one asset record and determines whether the combination of conditions creates actual exploitable exposure or whether defenses are holding.
This is the toxic combination engine. A CVE alone is a finding. A CVE on a reachable asset with degraded endpoint protection and a misconfigured network control facing an active threat group is an exposure. The Exposure Lens knows the difference.
Agents are the Multiplier
The Exposure Lens gives agents the context they need to reason accurately. The Agentic Engine gives them the ability to act on it. Here is how the four stages work in practice.
Detect. Agents evaluate every exposure signal as it emerges. Not on a scan cycle. Not when someone logs in. Continuously. A new CVE gets published. A configuration drifts. A control degrades. An asset changes state. Each change is a trigger. The agent picks it up and starts working.
Investigate. The agents run a full investigation against the Exposure Lens. It checks exploitability conditions. Validates compensating controls. Assesses whether active threat groups are targeting this specific weakness. Correlates asset criticality and business context. What would take an analyst 30 to 60 minutes per investigation happens in under four minutes, saving on average 160 investigation hours montly.. Findings that are not true exposures get filtered out with documented reasoning. No analyst time wasted.
Remediate. Validated exposures become operational cases. Each case includes root cause analysis, affected assets, a remediation path tailored to the existing stack, and automatically assigned ownership based on asset responsibility. Tickets are created and routed into ServiceNow, Jira, or your existing workflow. Full context attached. No chasing owners. No rebuilding the story in every handoff.
Verify. This is where the architecture diverges from everything else on the market. Agents confirm the fix actually eliminated the exposure. They continuously recheck as environments evolve. If conditions drift, a configuration changes, or a control degrades, the case reopens automatically. Exposure stays closed. Not just ticketed.
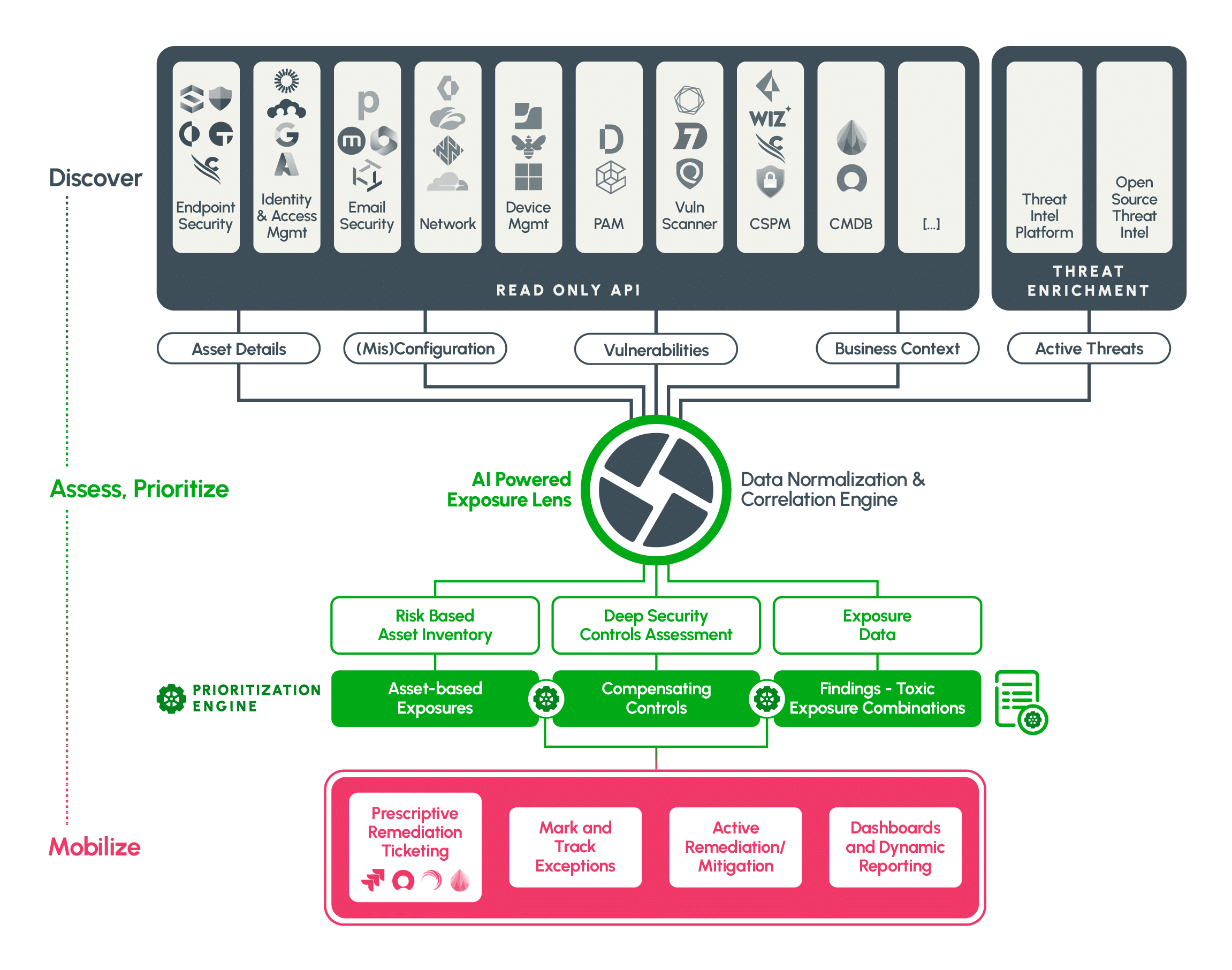
Why context is the hard part. Not the agent.
Here is something the industry is getting wrong right now. Everyone is racing to ship agents. The assumption is that the agent is the differentiator. Build a smarter agent. Give it a bigger context window. Connect it to more tools.
The agent is not the hard part.
The hard part is the context the agent reasons across. An agent without normalized, correlated, deduplicated exposure context will hallucinate. It will produce shallow analysis. It will give answers that sound right but miss the compensating control that changes the entire risk picture.
Consider what it takes to answer a simple question: ‘Is this asset actually exposed?’ You need the vulnerability data. The asset inventory. The network topology. The control configurations across EDR, firewall, WAF, and IAM. The threat intelligence. The business criticality. And you need all of it resolved, deduplicated, and current.
No single scanner provides that. No single cloud platform provides that. No million-token context window can hold it all for a large enterprise with 100,000+ assets and hundreds of millions of findings.
Nagomi has been building this context layer for years. Not weeks. Not since a funding announcement. The Exposure Lens represents years of integration work, normalization logic, control effectiveness mapping, and production deployment across enterprise environments. That is the foundation agents need to produce accurate, actionable output.
The question every security leader should ask any vendor shipping agentic capabilities: what context is your agent reasoning across? If the answer is ‘our own product’s data,’ the agent sees a partial picture. If the answer is ‘raw API calls to your tools at query time,’ the agent is building context on the fly and hoping for the best.
Operating across teams. Not inside one silo.
Exposure does not respect organizational boundaries. A vulnerability in an application might require a patch from engineering, a compensating control from the network team, a configuration change from cloud ops, and a risk acceptance decision from GRC. In most organizations, that coordination happens through email threads and spreadsheet handoffs.
Agentic Exposure Ops operates across SecOps, VulnerabilityManagement Offensive Security, GRC, IT, and Security Engineering. Cases are routed to the right owner based on asset responsibility. Every team works from the same exposure context. Same priorities. Same definition of what ‘resolved’ means. Shared visibility into what is open, what is in progress, and what has been verified closed.
This is not just a workflow improvement. It changes the operating model. Security teams stop generating lists and throwing them over a wall. Every team involved in remediation works from one shared picture with clear ownership and verified outcomes.
What this looks like in production
Let me share three real moments from our design partner deployments.
The invisible endpoint
One of our design partners had the agent flag a single endpoint loaded with problems. High severity. Multiple findings stacked. The team investigated and discovered it was a VDI box that nobody was even using. The fix was to turn it off. That was it. Without the agent correlating across their tools, that asset was invisible in a sea of 200,000+ vulnerabilities. The team would never have found it through manual triage. The agent surfaced it because it correlated the signals, not because any single scanner ranked it high enough to matter.
The wildcard DNS story
Same team. The agent flagged an asset as externally exposed. The security lead pushed back. He was confident the asset was internal. The agent came back with evidence from Qualys showing a wildcard DNS entry was assigning the asset an external IP address. Severity got adjusted. But then the agent found the Qualys agent on that endpoint was missing, so scans were not updating. Not as bad as they thought on one front. A new set of problems uncovered on another. Then the agent found other endpoints with the same wildcard DNS issue.
The compound exposure
At a Fortune 500 customer, Office EDR protections quietly drifted across hundreds of endpoints. The agents noticed and investigated. No alert. Five days before the incident, CVE-2026-21514, a Microsoft Word auth bypass actively exploited in the wild, landed on CISA KEV. Dozens of endpoints became vulnerable. The agent noticed and investigated. Still no alert. Because signals alone are not exposure. Then one device entered Reduced Functionality Mode in CrowdStrike. Internet-facing. Shallow EDR protections. Drifted compensating controls. An actively exploited vulnerability. A critical business unit. Now the signals compounded into real, exploitable exposure. Only then did the agent raise an urgent incident with full context and direct mobilization to the right owners.
That is what investigation looks like when the agent reasons across the full context. It does not just accept the first finding. It pulls the thread. It cross-references. It finds the thing behind the thing.
The funnel effect at scale
Here is what the pattern looks like at scale. A new CVE drops. CVSS 9.8. Your scanner picks it up across 340 assets. In a traditional workflow, that becomes a spreadsheet. An analyst starts investigating. Asset by asset. Console by console. Thirty minutes per investigation if they are fast.
In Nagomi, the agent fires within minutes. It correlates the CVE against the Exposure Lens. Of those 340 assets, 280 have compensating controls that effectively mitigate exploitation: properly configured WAF rules, network segmentation that blocks the attack vector, EDR policies that detect the exploitation technique. The agent documents the reasoning for each and suppresses those findings. No ticket. No noise.
The remaining 60 assets have genuine exposure. Of those, 12 are internet-facing, run business-critical workloads, and face active targeting from threat groups known to exploit this CVE family. Those 12 become priority cases. Each case includes the full investigation: why this asset is exposed, which controls are failing, what the remediation path looks like, and who owns the fix. Tickets are created. Owners are notified. The remediation clock starts.
When a fix is applied, the agent verifies the control posture changed. It rechecks the asset against the Exposure Lens. It confirms the compensating controls are now in place. If they are, the case closes with a verified resolution. If something drifts next week, the case reopens.
340 findings became 12 actionable cases. Zero analyst hours spent on triage.
What the customer data showed us
We started the gradual rollout of the agentic engine with our customers. Here is what we have seen in the first weeks of production deployment on average per customer.
| 1,716CVE investigations in 14 days | 4 minAverage investigation time | 80%Triage eliminated | 2+ FTEsCapacity returned |
And these are early numbers. The system improves as the Exposure Lens absorbs more context from the environment.
But the numbers only tell part of the story. What matters more is what changed operationally.
One customer went from spending their entire week manually cross-checking tools and compiling findings to spending about an hour a week reviewing open cases. Their words: “you do not have to babysit all the other tools anymore. The time they got back?” They are building automation playbooks they never had bandwidth for. The classic problem of needing automation to build automation, finally broken.
Another design partner, a multi-country bottling operation with a sprawling infrastructure footprint, saw the agentic engine as replacing the need to hire three to four additional analysts. They started calling their internal function ‘Exposure Ops’ before we even asked them to. That is category validation you cannot manufacture.
A third completed the full closed loop in production for the first time. Agents detected an exposure. Raised a case. The analyst approved the recommendation. A ticket was created. The issue was fixed. The agent verified the resolution held. End to end. That is the moment we built toward.
What’s ahead
This is the beginning. The agentic engine will continue to expand across remediation types, integration depth, and autonomous action capabilities. We are building toward an architecture where every security practitioner gains leverage through specialized agents that operate across the full exposure lifecycle.
The roadmap includes deeper remediation automation (agents that do not just recommend fixes but execute them through governed workflows), expanded control effectiveness benchmarking against specific threat actor TTPs, and broader federation capabilities for organizations running multiple agent systems.
But the foundation is what matters most. The Exposure Lens. The closed-loop architecture. The verified elimination model. Those are not features you bolt on later. They are the infrastructure that makes everything else trustworthy.
The operating model shift
When we started building Nagomi, we had a thesis: security teams do not lack technology. Their tools lack alignment. Exposure persists in the gaps between tools. We set out to close those gaps.
The Exposure Lens was the first step. Correlate the signals. Unify the view. Give teams one picture of what is actually exposed. That foundation took years to build. Normalization logic across dozens of integrations. Control effectiveness mapping that holds up in production. The kind of infrastructure work that does not make for exciting demos but makes everything on top of it trustworthy.
The agentic engine is the second step. It takes that foundation and puts it to work autonomously. The results from our design partners confirmed what we believed: when agents have the right context, they do not just triage faster. They change the operating model entirely. Analysts stop investigating and start reviewing. Teams stop generating lists and start closing exposure. And exposure stays closed because the system verifies it continuously.
The security industry is at an inflection point. The question is not whether AI will participate in security operations. It is whether the architecture around the AI is built to produce trustworthy outcomes.
Agentic Exposure Ops is our answer. A closed-loop operating model where agents detect, investigate, remediate, and verify. Where context is the foundation and agents are the multiplier. Where exposure does not just get found. It gets eliminated. And it stays eliminated.
You set priorities. Agents handle the rest.