back to blog
BLOG March 13, 2026
What is Preemptive Exposure Management?From Visibility to Action
Nagomi Security

Table of Contents

What is Preemptive Security? From Visibility to Action
Preemptive exposure management (PEM) is a cybersecurity approach that uses AI-driven technology to find, validate, and remediate exposures before attackers can exploit them. It goes beyond traditional exposure management by automating the entire lifecycle from discovery through resolution. Where traditional approaches stop at visibility, preemptive exposure management closes the loop with autonomous action.
Gartner introduced preemptive exposure management in its February 2026 research as the next evolution of how organizations handle risk. The argument is direct: in an age of AI-driven, subsecond exploitation, simply “managing” exposure is not enough. Organizations must interdict it. Here is what that means and how the shift is taking shape.
Preemptive Exposure Management, Defined
Preemptive exposure management accelerates every stage of the exposure lifecycle. It systematically disrupts and denies adversary behavior by automating the identification of attack paths, simulating adversary techniques, and closing exposures before they are weaponized.
The “preemptive” distinction matters. Traditional exposure management finds problems and reports them. Preemptive exposure management finds problems, confirms they are real, and fixes them. The difference is the distance between a vulnerability report and a resolved risk.
Gartner frames PEM as the convergence of three capabilities: AI-driven exposure discovery and prioritization, automated validation of exploitability, and autonomous interdiction of confirmed risks. All three must work together. Any gap in the chain leaves exposure unresolved.
Why Traditional Exposure Management Falls Short
Exposure management has matured in tooling, not in outcomes.
Most security organizations now run vulnerability scanners, attack surface management platforms, and some form of risk prioritization engine. Findings are not the constraint. Execution is.
Nagomi’s Illusion of Maturity: 2026 Enterprise Exposure Snapshot found that 91% of assets pass vulnerability assessments, yet more than 75% of organizations have gaps in core security controls such as MFA, EDR configuration, and endpoint policy enforcement. Identity and endpoint controls pass at roughly 50%, and only about 30% of assets show strong control coverage across identity, endpoint, and awareness simultaneously.
Traditional exposure management treats vulnerabilities as the primary signal of risk. But risk does not accumulate evenly. It concentrates where controls fail together.
After correlation, most environments do not show thousands of equally urgent problems. They collapse into roughly seven high-impact exposure conditions, often driven by a single degraded control or misconfiguration affecting thousands of assets. These conditions frequently sit outside standard vulnerability scoring models, which is why dashboards improve while attacker pathways remain intact.
Traditional models generate findings and prioritize lists. They do not reconcile how assets, controls, vulnerabilities, and threats interact at the same time. They measure progress at the tool level, while exposure forms at the intersection of tools.
The result is predictable. Teams move tickets. Dashboards trend positively. Operational latency persists. And exposure survives longer than it should.
That gap between signal and coordinated action is where traditional exposure management falls short.
Visibility Without Action Is Just Observation
Knowing you have a problem is not the same as fixing it. Many organizations have invested heavily in exposure visibility, covering external attack surface management (EASM), cyber asset attack surface management (CAASM), vulnerability assessment, and security control assessment. These tools produce accurate, comprehensive views of organizational risk.
But visibility without remediation is observation. As Gartner states in its February 2026 research, exposure management must evolve from a framework of observation to an architecture of interdiction. The industry has solved the “find it” problem. Now it needs to solve the “fix it” problem at the same speed.
The Remediation Bottleneck
Security teams discover exposures at machine speed but remediate them at human speed. Scanners generate thousands of findings. Prioritization tools rank them. Then the process stalls. Remediation requires coordination across security, IT operations, DevOps, and application teams. Ownership is unclear. Timelines stretch. The backlog grows.
Autonomous Interdiction: The Core of Preemptive Exposure Management
Meanwhile, attackers do not wait. AI-enabled threats compress exploitation timelines from days to hours to minutes. The window between discovery and remediation is where breaches happen. Traditional exposure management documents that window. Preemptive exposure management closes it.
Autonomous interdiction is what separates preemptive exposure management from everything that came before it. It is the automation of the fix itself, not just the automation of the workflow around the fix.
There is an important distinction here. Automated remediation workflows route findings to the right team, create tickets, and track progress. That is valuable but incomplete. Autonomous interdiction goes further. It enables systems to directly resolve exposures: isolating compromised hosts, disabling unnecessary ports and services, restricting access, revoking credentials, terminating risky sessions, and rolling out configuration changes.
This requires a shift from human-in-the-loop to human-on-the-loop operations. Security teams move from approving every action to setting policies, defining boundaries, and overseeing autonomous systems that execute within those guardrails.
True automated remediation is not just automating manual workflows or handling repetitive tasks. It is the automation of the fix itself. The system does not file a ticket. It resolves the exposure. That is the line between exposure management and preemptive exposure management.
How AI Powers the Preemptive Lifecycle
Preemptive exposure management depends on AI at every stage. Manual processes cannot operate at the speed or scale this model requires.
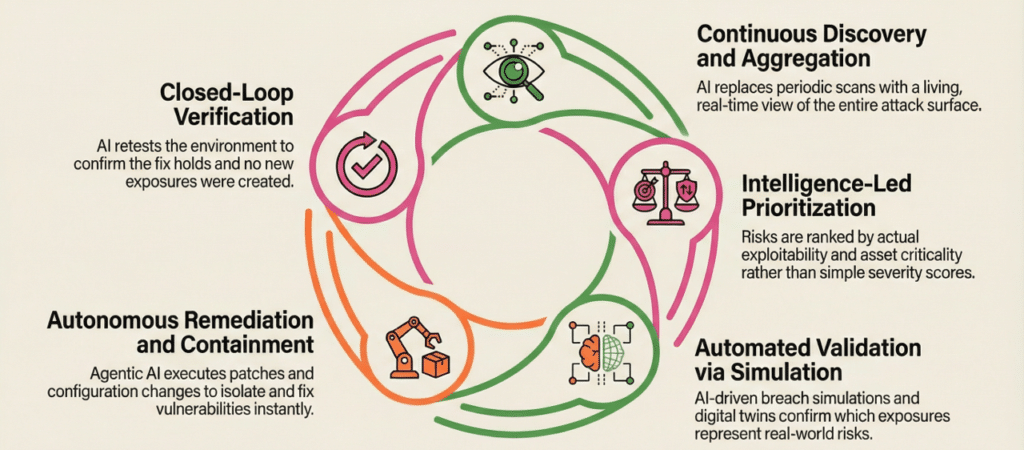
Discovery and aggregation. AI continuously discovers, aggregates, and normalizes exposure data across the full attack surface. It connects findings from disparate tools and correlates them with business context, asset criticality, and threat intelligence. This replaces periodic scans with a living, continuously updated view of organizational risk.
Prioritization. AI ranks exposures by actual exploitability, not just severity scores. It factors in the current state of security controls, the presence of compensating measures, and the real-world likelihood of exploitation given the threat landscape. A critical CVE that your controls already block drops in priority. A medium-severity misconfiguration that creates an open attack path to a crown jewel asset rises.
Validation. AI-driven simulation tests whether exposures can actually be exploited. This includes automated breach and attack simulation, penetration testing, and red team exercises. Digital twins model attacker behavior against current configurations to confirm which exposures represent real risk and which are theoretical.
Remediation. Agentic AI executes containment and remediation actions autonomously. It pushes configuration changes, patches vulnerable systems, revokes excessive access, and isolates compromised assets. Impact previews and rollback capabilities build confidence. Semi-automated modes let teams validate outcomes before moving to full autonomy.
Verification. After remediation, AI confirms that the exposure is actually closed. It retests the environment to verify that the fix holds and that no new exposures were introduced. This closes the loop completely, from finding to finishing.
What Changes for Security Teams
Preemptive exposure management does not eliminate the need for security professionals. It fundamentally changes what they do.
From execution to oversight. Security teams shift from hands-on remediation to governing autonomous systems. They define policies, set boundaries for automated action, review exceptions, and handle the edge cases that require human judgment. The daily work moves from triaging alerts to tuning the system that triages them.
From reporting to operating. Exposure management becomes an operational function, not a reporting one. Instead of producing quarterly vulnerability reports, teams run a continuous exposure reduction program. Automated workflows assign ownership, coordinate action, and track resolution. The operating model becomes: find it, validate it, fix it, confirm it. Every cycle.
From time-to-patch to Mean Time to Neutralize. Success metrics change. Time-to-patch measures one narrow remediation path. Mean Time to Neutralize (MTTN) captures the full picture: how quickly the organization actually mitigates a confirmed risk, whether through patching, configuration changes, compensating controls, or containment. With autonomous systems, MTTN compresses from hours to milliseconds.
From tool management to ecosystem governance. No single vendor will deliver complete preemptive exposure management. Organizations will orchestrate ecosystems of specialized tools, agents, and platforms. The security team’s role shifts toward integration, governance, and ensuring that autonomous components work together reliably.
Building Trust in Autonomous Remediation
The biggest barrier to preemptive exposure management is not technology. It is trust. Security teams are cautious about letting systems make changes autonomously, and for good reason. A misconfigured automated action can cause more damage than the exposure it was meant to fix.
That caution is intensifying.
Our CISO Pressure Index shows AI is now pressuring security leaders from both directions.
59% cite agentic AI as their leading near-term threat, and nearly 20% of recent incidents already involve AI. At the same time, 82% report pressure from executives or boards to reduce staff through AI-driven automation.
CISOs are being told AI is the problem and the solution.
That tension reshapes the trust conversation. Teams cannot rely on fully manual remediation models when AI-driven threats compress the exposure window. But they also cannot accept opaque automation that makes changes without accountability. When staffing pressure meets operational risk, autonomous remediation has to earn its authority.
The path to trust follows a predictable pattern. Organizations start with impact previews that show what an automated action would do before execution. They operate in semi-automated mode where the system recommends actions and humans approve them. As confidence builds, low-risk remediations move to full autonomy while high-impact changes retain human oversight.
Transparency is non-negotiable. Agentic reasoning steps must be visible and auditable. Teams need to understand why a system took a specific action, what data informed the decision, and what the expected outcome was. AI TRiSM principles, covering reliability, explainability, and privacy, provide the governance guardrails.
Industry-specific approaches are emerging. Financial services organizations are implementing tiered autonomy with logic-gate models that match the level of automated action to asset risk. Healthcare organizations are deploying sidecar security architectures that protect sensitive systems without modifying them directly. Manufacturing and utilities are adopting immutable endpoint strategies where devices are replaced rather than patched.
The CISO Pressure Index makes the stakes clear. AI-driven threats are accelerating. Executive pressure to automate is rising. Trust becomes the hinge point between those forces.
Autonomous remediation does not succeed because it moves fast. It succeeds because it moves fast with control, visibility, and verification.
Exposure Ops: The Operating Model Behind Preemptive Exposure Management
Preemptive exposure management is a technology capability. Exposure Ops is the operating model that makes it work. The distinction matters. Without the right operational foundation, even the most advanced autonomous systems produce findings that stall in the same handoff gaps they were designed to eliminate.
Exposure Ops treats exposure reduction as a continuous operational discipline, not a periodic reporting exercise. Every validated exposure follows a defined path: discovered, prioritized, assigned, remediated, verified. No stage is optional. No finding sits in a queue without an owner. No resolution is assumed without confirmation.
This is where most organizations break down today. They generate findings faster than they can act on them. Scanners, validators, and prioritization engines all do their jobs. Then the output lands in a spreadsheet. Ownership is negotiated over email. Timelines slip. The backlog compounds. The gap between finding a problem and fixing it becomes the gap attackers walk through.
Exposure Ops closes that gap by connecting three things that are usually disconnected: the teams responsible for remediation, the workflows that coordinate their actions, and the data that measures whether risk actually went down.
In practice, this means automated workflows that assign ownership the moment a validated exposure is confirmed. It means cross-team coordination between security, IT, DevOps, and application teams with clear accountability at every step. It means measuring reduction in validated exposure over time, not counting patches applied or scans completed.
The cultural shift is just as important as the technical one. Gartner notes that preemptive exposure management will not displace security teams but will transform their responsibility from hands-on execution to oversight. Teams accustomed to manually triaging every finding must learn to set policies, define guardrails, and trust systems to execute within them. The daily work moves from doing the remediation to governing the system that does it.
Organizations that treat exposure reduction as an operational function, with the same rigor they apply to incident response or change management, will be the ones that actually close the loop. From finding to finishing. That is what Exposure Ops delivers.
Why This Matters Now
The case for preemptive exposure management comes down to a simple math problem. Exposures are growing faster than teams can remediate them. Attackers are automating faster than defenders are. The gap between finding a problem and fixing it is where breaches happen.
Security teams do not lack tools. Most organizations run dozens of them. The problem is the operating model. Exposure persists in the gaps between tools, in the manual handoffs between teams, and in the lag between discovery and resolution. Preemptive exposure management closes those gaps by connecting the full lifecycle: from finding to finishing.
Gartner’s research confirms the industry is heading this direction. The frameworks, the technology, and the data all point the same way. Organizations that begin building toward autonomous exposure resolution now will be positioned to operate at the speed their threat environment demands. Those that wait will continue documenting breaches instead of preventing them.
Frequently Asked Questions
What is preeemptive exposure management
Preemptive exposure management (PEM) is a cybersecurity approach that uses AI-driven technology to find, validate, and remediate exposures before attackers can exploit them. It goes beyond traditional exposure management by automating the entire lifecycle from discovery through resolution, including autonomous interdiction where systems fix problems without waiting for human approval.
How is preemptive exposure management different from traditional exposure management?
Traditional exposure management identifies and prioritizes vulnerabilities, then hands off remediation to other teams. Preemptive exposure management closes the loop. It validates whether exposures are actually exploitable, autonomously remediates confirmed risks, and measures reduction in real exposure over time. The key difference is that PEM acts on findings instead of just reporting them.
What is autonomous interdiction in exposure management?
Autonomous interdiction is the automated remediation of exposures without requiring human approval for each action. It includes isolating compromised hosts, revoking credentials, disabling unnecessary ports, rolling out configuration changes, and terminating risky sessions. Gartner identifies autonomous interdiction as a requirement for preemptive exposure management.
What is Mean Time to Neutralize ( MTTN)?
Mean Time to Neutralize is an emerging metric that measures how quickly an organization actually mitigates a confirmed exposure, whether through patching, configuration changes, or compensating controls. It replaces traditional metrics like time to patch by capturing the full remediation lifecycle. With autonomous systems, MTTN can compress from hours to milliseconds.
When will preemptive exposure management become mainstream?
Gartner projects that by 2029, 60% of unified exposure management solutions will incorporate domain-specialized automated mitigation and remediation capabilities. The evolution is already underway, with automated workflow orchestration available today, agentic AI capabilities emerging in the near term, and domain-specialized autonomous ecosystems expected within three to eight years.
Gartner, “Emerging Tech: The Future of Exposure Management Will Be Preemptive, Driven by Autonomous Interdiction,” Elizabeth Kim, Luis Castillo, Isy Bangurah, Travis Lee, 13 February 2026, ID G00845340.
Gartner, “Emerging Tech: The Global Attack Surface Grid Demands Unified Exposure Management,” Luis Castillo, David Senf, Tom Powledge, 27 September 2025, ID G00817531.
Gartner is a registered trademark of Gartner, Inc. and its affiliates. This content references Gartner research for informational purposes. Inclusion in Gartner research does not constitute endorsement.