back to blog
BLOG Nov 14 2025
How One Hospitality Enterprise Unified Exposure Management Across Four Security Teams
Nagomi Security

Table of Contents
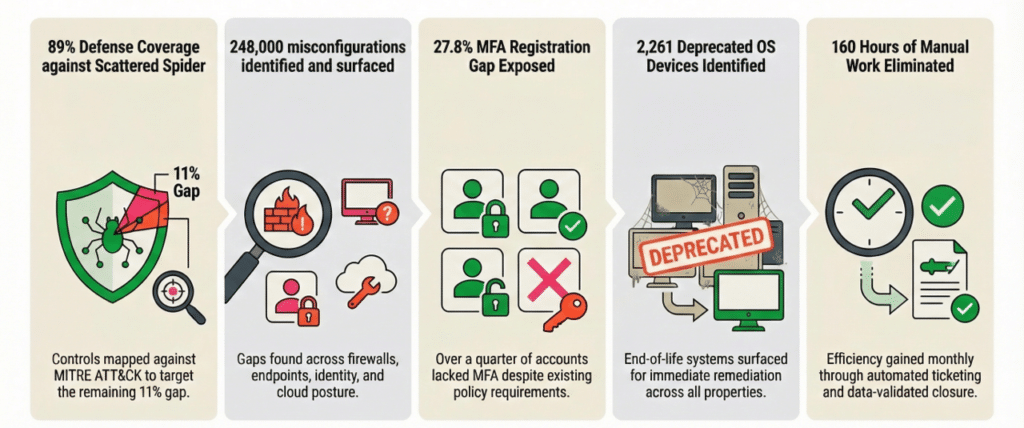
A large hospitality and gaming enterprise with four separate security teams had no shared view of exposure across its properties. Each team operated from different data, different tools, and different definitions of what mattered. After deploying Nagomi as its exposure management platform, the organization achieved 89% defense coverage against specific threat techniques, identified 248,000 misconfigurations across 1.4 million configuration checks, and eliminated approximately 160 hours of manual remediation work per month. This is how they did it.

Four Teams, Zero Shared Operating Picture
This company operates dozens of properties across the United States. Gaming floors. Hotels. Entertainment venues. Each location runs its own infrastructure, its own systems, its own IT staff.
Four teams shared responsibility for security. None of them shared a view of what was actually exposed.
The offensive security team owned vulnerability management and penetration testing. SecOps managed detection coverage and control effectiveness. GRC measured the program against compliance frameworks. Property IT handled patching and configuration on the ground. Each team operated from different data, different tools, and different definitions of what mattered.
When offensive security flagged a critical vulnerability, there was no fast way to verify whether endpoint detection was active on the affected asset, whether the control configuration was correct, whether GRC had accounted for it, or whether property IT had applied the fix. The tools were not the problem. The organization had invested in Rapid7, CrowdStrike, Wiz, Palo Alto Panorama, and Microsoft Entra ID. Each tool generated findings. None of them correlated those findings at the asset level in a way that connected vulnerabilities to control coverage to configuration state.
The result was four teams working in parallel, each with a partial picture, none of them able to answer a simple question: are we actually protected?
When Manual Remediation Fails, Exposure Compounds
A single Microsoft Patch Tuesday update might remediate 100 CVEs. Under the existing model, the offensive security team had to create 100 individual tickets, identify which property IT teams owned the affected assets, route each ticket separately, and hope someone on the other end actually applied the fix. Hundreds or thousands of tickets a month. Each manually created. Manually routed. Manually tracked. That is not a remediation model. That is a backlog generator.
Even when tickets got closed, closure proved nothing. Someone updated a status field, but nobody validated that the vulnerability was actually remediated, that the configuration was corrected, or that coverage was restored. The offensive security team could not distinguish between a ticket closed because the patch worked and one closed because someone clicked a button. The 2024 Verizon Data Breach Investigations Report found that median time to remediate known vulnerabilities across enterprises exceeds 55 days, and this organization was no exception.
Exposure was persisting. The backlog was growing. And then Scattered Spider hit the industry.
The Threat That Made the Gaps Impossible to Ignore
In September 2023, Scattered Spider breached two of the largest casino and hospitality operators in the United States. One lost an estimated $100 million, according to Bloomberg reporting. The other paid a $15 million ransom, as disclosed in SEC filings. Both attacks started with social engineering, escalated through identity systems, and ended with ransomware deployed across production infrastructure.
This was not an abstract threat. This was the same adversary, targeting the same industry, using techniques mapped to MITRE ATT&CK that exploit exactly the kinds of gaps this organization had: inconsistent MFA enforcement, fragmented visibility across identity and endpoint systems, and no way to map control coverage against specific attack techniques.
The offensive security team knew Scattered Spider was a priority. But there was no systematic way to assess which adversary techniques their controls actually covered, where detection gaps existed, or how quickly those gaps could be closed. The four-team operating model that made remediation slow also made threat benchmarking impossible.
They needed a different approach.
Why Traditional RBVM Tools Could Note Help
The team evaluated modern vulnerability management solutions. Every platform they looked at solved the same narrow slice: better prioritization for one team, better dashboards for one view. None of them connected vulnerability findings to control effectiveness, configuration state, or identity exposure at the asset level. No shared operating picture across four teams.
Traditional vulnerability management platforms prioritize by CVSS score or asset criticality, answering the question “what is vulnerable?” but not “are our controls already compensating for this exposure?” That distinction matters. If an endpoint detection rule already blocks the exploit path for a given CVE, that vulnerability is a lower operational priority than one with no compensating control in place. This is the core principle behind Automated Security Control Assessment (ASCA), the capability that separates an exposure management platform from a vulnerability scanner.
This is also a recognized gap across the industry. According to Gartner, fewer than 5% of organizations have operationalized their exposure management programs to this level of cross-team integration, which is why they identified Continuous Threat Exposure Management (CTEM) as a top strategic technology trend. The problem was not unique to this organization. The solutions available to them were.
That search led them to Nagomi.
One Exposure Operations Layer for All Four Teams
Nagomi ingested data from tools across their stack, normalizing and deduplicating findings at the asset level, correlating CVEs across multiple scanners and matching them to the same asset with full context on control state, configuration posture, and coverage status. Not a vulnerability dashboard for one team. A correlated exposure layer that connected vulnerabilities, coverage gaps, misconfigurations, identity exposure, and control effectiveness into one operating picture for all four teams.
The impact looked different for each group. For offensive security, CVSS-only prioritization was replaced with toxic combinations: assets where critical vulnerabilities overlap with missing controls, configuration drift, and business context. For SecOps, continuous assessment replaced periodic audits, with real-time visibility into which endpoint agents were active, which firewall policies had gaps, and where detection rules were missing. For GRC, the same data offensive security used to prioritize vulnerabilities fed directly into risk registers, audit reporting, and framework alignment metrics. For property IT, patch-based ticketing replaced CVE-per-ticket chaos: one patch that remediates 100 CVEs becomes one ticket, automatically split by property, routed with full context, and tracked to validated closure.
“We went from four separate views of risk to one shared picture of exposure. That changed how fast we could move.”
Director of Offensive Security, hospitality enterprise customer
Results: Coverage, Configuration, and Remediation
What This Means for Security Leadership
Before Nagomi, leadership reporting was a patchwork. The CISO assembled point-in-time snapshots from each team, reconciled conflicting numbers, and presented a narrative only as reliable as the weakest data source.
Now leadership gets a single, continuous, data-backed exposure briefing. When they ask whether the organization is protected against Scattered Spider, the answer is 89% coverage measured against specific adversary techniques, with a defined plan to close the remaining gaps. Budget justification became concrete. Cross-team friction decreased. Remediation acceptance improved because every ticket carries full context: what to fix, why it matters, what threat actor technique it maps to, and how to verify the fix worked.
Four teams. One exposure truth. Everything moves faster.
What Is Exposure Ops?
Exposure Ops is the operating discipline that continuously evaluates attacker-relevant exposure, prioritizes it based on business criticality and defense effectiveness, drives structured remediation, and verifies that elimination holds as environments change.
Security teams run dozens of tools that each find something. Scanners find vulnerabilities. EDR finds threats. SIEM collects logs. But no single tool reconciles all of that output into a prioritized action plan. That gap is where exposure persists, and where incidents start.
Nagomi’s Agentic Exposure Ops Platform connects to the existing security stack, assesses whether controls actually cover the exposures those tools surface, and automates the path from finding to confirmed resolution. For this hospitality enterprise, that meant replacing spreadsheet-based coordination across four teams with a single platform that correlates vulnerabilities, control effectiveness, configuration state, and identity exposure at the asset level. Faster exposure reduction. Fewer preventable escalations. Measurable team capacity returned through agent-driven investigation and validation.
Four teams. One platform. 89% coverage against a live adversary threat. Book a demo and see how Nagomi makes it possible.