
The security industry has no shortage of blueprints. Between the NIST CSF, MITRE ATT&CK, and others, practitioners have spent decades codifying how a secure environment should look. These frameworks are the essential vocabulary of modern risk; they provide the benchmarks that boards understand and auditors demand.
The problem is that a framework is a map, not the journey. Most organizations face a massive execution gap between the “ideal state” described by NIST and the technical reality of their production environments. Configurations drift. Controls degrade. Coverage assumptions go stale. And the gap between what the framework outlines and what the environment enforces becomes the largest contributor to unmanaged cyber risk.
To move from checking boxes to actual risk reduction, organizations must shift toward Threat Exposure Management (TEM), a holistic approach that focuses on how assets, controls, and threats intersect and, crucially, how those exposures are actually fixed.
Why Configuration Drift Is the Hidden Driver of Cyber Risk
SecOps teams expend significant energy to keep pace with a dynamic attack surface. Between cloud migrations, SaaS sprawl, and hybrid workforce shifts, the volume of tuning required to stay compliant has become overwhelming. It’s not a lack of effort that’s contributing to this problem. It’s the challenge of managing thousands of agents, policies, and alerts across siloed consoles.
In and amongst all the things that happen daily to keep networks up, running, and relatively secure is configuration drift. Configuration drift is not intentional; it’s what happens when a firewall rule is temporarily relaxed during a deployment but, inadvertently, never restored to its previous state; an EDR agent stops reporting on a subset of endpoints but not remediated; an identity provider policy is loosened for a migration and never reverted. Each of these changes seems small in isolation, but configuration drift happens slowly, without documentation, and the scale of exposure spins beyond acceptable, reopening the exposure pathways that framework-aligned programs are specifically designed to close.
Left unmanaged, drift turns compliant environments into risky ones. To ensure configurations don’t run afoul of intent, SecOps teams need continuous visibility into how their controls are operating (not just during a point-in-time audit), how that mapping degrades over time, and what that all means for risk posture.
How to Align Exposure Management with NIST CSF and MITRE ATT&CK
A resilient defense requires framework signals to work in concert rather than in isolation. NIST CSF and MITRE ATT&CK answer different questions, and mature exposure management programs need both.
NIST CSF provides the structural lifecycle. It defines the governance model, the functions (Identify, Protect, Detect, Respond, Recover, and Govern), and the controls that must be continuously monitored. It’s the lens through which boards and auditors view program maturity.
MITRE ATT&CK provides the adversary perspective. It describes how threat actors behave, the tactics, techniques, and procedures (TTPs) they use, and the defensive coverage required to detect and disrupt each stage of an attack.
Together, these frameworks let security teams ask the right question: How does each deployed control help defend against the real-life TTPs, and will that control hold in our environment?
Using this method helps teams shift from checkbox compliance to essential exposure management. Rather than tracking whether a control exists, SecOps teams track whether the control is configured, active, and effective against the techniques adversaries are most likely to use.
How Frameworks Help Operationalize Exposure Management
Frameworks are effective only when they drive action rather than documentation. To optimize frameworks. SecOps teams can tune controls to align with their unique environment.
Resilient defense strategies implement cross-framework coordination to reduce the time between risk identification and active mitigation:
- CIS18: Establishes the foundation for essential hygiene to ensure technical controls are correctly configured and hardened across the environment.
- MITRE ATT&CK: Provides context for adversary behavior and details threat actor techniques after an initial exploit.
- NIST CSF 2.0: Offers the structural lifecycle to ensure these activities are part of a well-maintained, continuous process.
Nagomi ties existing security controls to frameworks like those mentioned above. The platform helps teams identify which MITRE techniques are exposed to current threat actor campaigns and misconfigurations, but doesn’t require SecOps teams to perform manual correlation at the vulnerability level. This method:
- Provides evidence of exposure coverage based on how deployed tools align with framework requirements
- Reduces the time between identifying risk and fixing exposures (mean-time-to-remediation)
- Improves teams’ abilities to respond to issues and ensure fixes remain closed
How Closed-Loop Remediation Helps Exposure Management
Closure only matters if it reflects the true state of the environment, not the status of a ticket. In many organizations, a “closed” ticket is an administrative event: someone clicks a button in a workflow tool, and the risk is presumed gone. Checkbox ticked.
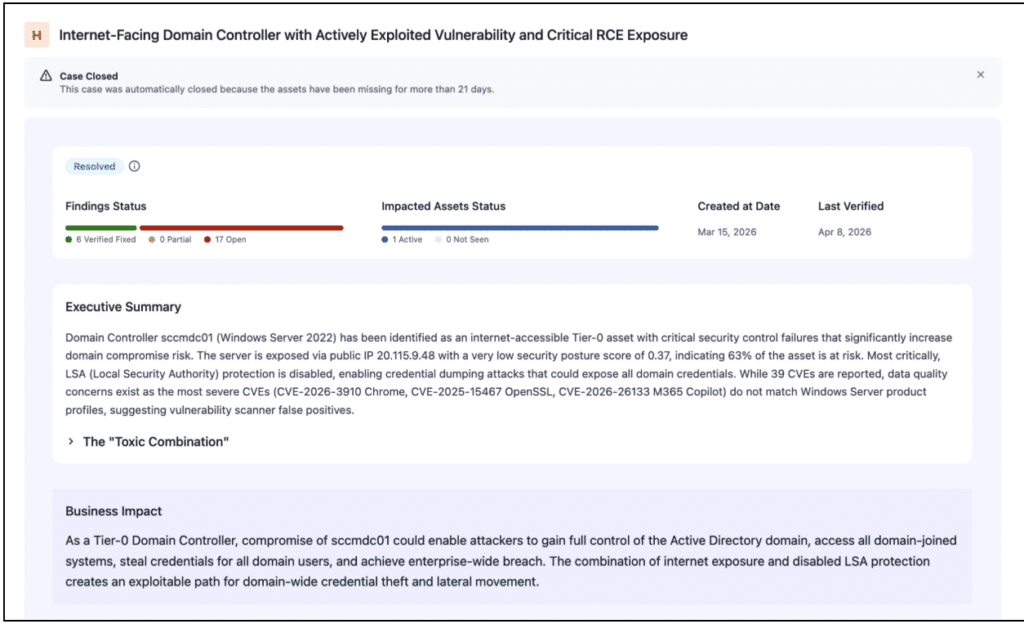
Nagomi shifts this process to focus on verified closure, meaning, the resolution of an exposure can be tied to what’s observed in the environment rather than what has been marked complete in a ticketing system. With the Nagomi platform, a finding is only considered closed once the underlying condition no longer exists. This creates a closed-loop verification process, and is unique to Nagomi’s platform.
This matters for three reasons.
- First, it produces structural proof of risk reduction that can be mapped back to NIST reporting obligations and MITRE ATT&CK coverage metrics.
- Second, it detects drift automatically. If a configuration reverts to an insecure state, the exposure reappears and the remediation loop reopens, rather than quietly falling off the radar because the original ticket was closed.
- Third, it prevents the “one-and-done” pattern where the same exposure is remediated, reintroduced, and remediated again without anyone noticing the cycle.
Close-loop verification is the only way to ensure that reintroduced risk results in remediation that, in turn, results in risk reduction.
Optimizing the Security Stack vs. Tools Acquisition
The traditional answer to new risks was to buy another tool. However, more tools often mean more complexity without greater security benefit. The priority for modern teams now needs to evolve from product acquisition to configuration optimization.
Optimization is about making the existing stack work smarter. When organizations use Nagomi to centralize the verification of security settings across NIST and MITRE-aligned controls, they achieve several goals at once:
- Maximize existing ROI by ensuring the features they already paid for are active and defending the environment
- Shrink the attack surface by preventing the toxic combinations that attackers rely on
- Operationalize the SOC by shifting analyst work from manual data assembly to strategic exposure analysis
A Practical Path for Continuous Coverage
Improving security risk posture should be a systemic, automated approach to the entire exposure lifecycle. With Nagomi, security ops teams can:
- Centralize the view and stop the search for configuration gaps in dozens of different places
- Map exposure to the NIST controls and MITRE ATT&CK techniques it affects
- Verify coverage continuously and close the loop on remediation with environment-level proof
- Move away from point-in-time audits to real-time risk checks that catch drift as it happens
The goal of exposure management is to ensure deployed tools actually manage exposures and drive down risk — which is also the intent of industry-leading frameworks like NIST and MITRE. By automating investigation and verification, Nagomi transforms a fragmented collection of tools into a cohesive, high-performance defense that aligns with frameworks to help businesses move beyond checkbox compliance into true, operational, and validated exposure management.
Is your security stack actually defending the environment, or is it just waiting for another manual update? Schedule a demo to find out.



