Table of Contents
Managing security across multiple subsidiaries is a balancing act leaders need enterprise-wide visibility without undermining business autonomy. In this blog, Nagomi’s Technical Success Manager, Tim Dickinson shares customer stories of how organizations use subsidiary reporting to preserve competitive boundaries, deliver accurate risk data to the right people, and improve remediation accountability. The result is security governance that scales with the business instead of working against it.

The Hidden Challenge of Multi-Business Security
As Nagomi Security’s Technical Success Manager, I spend a lot of time talking with enterprise security teams about their biggest operational headaches. And there’s one challenge that comes up again and again, especially with larger organizations: How do you maintain visibility and control across multiple business units without creating a compliance nightmare or stepping on operational toes?
It doesn’t matter if you’re managing a portfolio company, working through a post-acquisition integration, or running security for a shared services model, the fundamental problem is the same. You need consistent security outcomes across different businesses, but you can’t treat them all like they’re the same business.
I’ve watched customers wrestle with this for years, trying everything from spreadsheet gymnastics to forcing square-peg subsidiaries into round-hole security tools. Most of these approaches either break down at scale or create more problems than they solve.
But recently, I’ve been seeing a different pattern emerge, one that’s working really well for our customers who’ve implemented subsidiary reporting. Let me walk you through what I’m seeing in the field.
The Portfolio Problem: Separate but Not Equal
One of our customers runs a portfolio of tech companies, each operating in slightly different verticals. Some of these subsidiaries actually compete with each other, which created an immediate problem when they started thinking about centralizing security oversight.
The portfolio CISO needed visibility across all companies to manage group-level risk and report to the board. But the individual CEOs weren’t about to share competitive intelligence through a shared security dashboard, and frankly, they shouldn’t have to.
Their solution was elegant: they used Nagomi’s child organization structure to create clean separation while maintaining oversight. Each subsidiary operates as its own organization with local admin access limited to their security or IT teams. The parent organization maintains visibility into all of them but only directly manages a central shared services org.
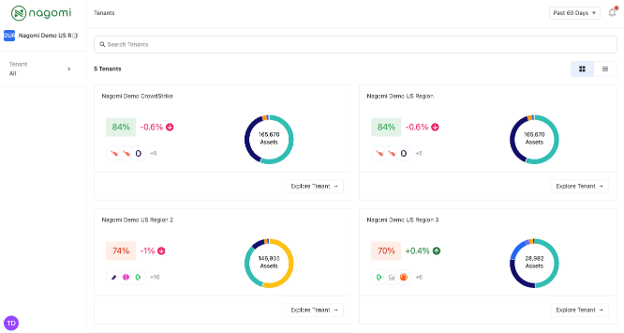
What I love about this setup is how it preserves the business realities while solving the security problem. Each company maintains complete autonomy over their security posture and remediation priorities, but the group CISO can still see portfolio-wide exposure trends and step in when a subsidiary needs support or when issues could impact the broader organization.
The Acquisition Integration Challenge: Messy Data, Clean Reporting
Another customer came to us in the middle of integrating several legacy acquisitions under a unified security program. These companies had been operating independently for years, each with their own tools, processes, and, let’s be honest, varying levels of security maturity.
When they started trying to roll everything up into enterprise-wide reporting, they hit a wall. The acquired companies had significant security gaps, and their lower exposure scores were dragging down the metrics for the entire organization. Suddenly, their executive dashboards were showing declining security posture even though the core business was actually improving.
They could have tried to massage the data or create complex filtering rules, but that would have compromised the integrity of their reporting. Instead, they spun up separate organizations in Nagomi for each business unit. Now each acquisition has its own exposure score, risk profile, and remediation roadmap, while the central security team can track progress and provide support without muddying their primary business metrics.
The result? Executive leadership gets accurate, actionable data about the core business, while the security team gets clear visibility into where each acquisition stands and what support they need to reach enterprise standards.
Why Purpose-Built Segmentation Matters
After watching dozens of customers work through these challenges, I’ve identified a few key benefits that show up consistently when organizations implement proper subsidiary reporting:
Business boundaries stay intact. Whether your teams need separation for competitive reasons, regulatory compliance, or just internal politics, subsidiary reporting creates those clean lines without adding operational overhead or forcing awkward workarounds.
The right data reaches the right people. Instead of overwhelming local teams with enterprise-wide metrics they can’t act on, or giving executives blended averages that don’t tell the real story, everyone gets a view that’s tailored to their scope and responsibilities.
Remediation becomes more effective. When you can assign security findings directly to the right business unit and track their progress independently, you eliminate confusion about ownership and accountability. Teams focus on what they can control, and escalation only happens when it’s actually needed.
Executive trust is maintained. Nothing undermines a security program faster than metrics that don’t make sense or seem disconnected from business reality. When exposure scores accurately reflect the actual risk profile of each business unit, executives can make informed decisions and track meaningful progress.
Making Security Work for Every Business Unit
The companies that are most successful with subsidiary reporting aren’t the ones trying to force organizational complexity into simple tools. They’re the ones who recognize that effective security governance requires structure that matches business reality.
If you’re managing security across multiple business units, whether through acquisition, shared services, or portfolio management, the question isn’t whether you need better segmentation. It’s whether your current approach is helping your teams succeed or just creating more work.
From what I’m seeing in the field, the organizations that get subsidiary reporting right are the ones that can scale their security programs without losing control, maintain trust with leadership without compromising on standards, and give their teams the autonomy they need to be effective.
That’s not just better security operations, that’s better business.
Watch our walkthrough or request a demo to see how we help teams surface what matters, skip the noise, and finally prove they’re protected.