back to blog
BLOG
The Importance of Compensating Controls: Stop Counting Gaps. Start Closing Exposure.

One of the most common complaints I hear from security leaders sounds like this: “Don’t show me all the gaps if you’re not accounting for the controls I’ve already put in place.”
It’s a fair point. And it points to a deeper problem. Most security programs are built to find and report. Very few are built to close. Compensating controls sit at the center of that gap.
What Are Compensating Controls?
Compensating controls are security measures put in place when a primary control, such as a firewall, encryption, or an intrusion detection system, is ineffective, impractical, or not feasible given budget, legacy infrastructure, or operational constraints.
They are not workarounds. They are deliberate layers of defense. Tighter access controls. Enhanced monitoring. Stricter segmentation. Manual verification where automation falls short.
The problem is that most organizations deploy compensating controls and then lose track of them. They run scans. They generate reports. They count gaps. They do not account for what is already absorbing risk. That creates a distorted picture of actual exposure.
What is the Importance of Compensating Controls?
Think of it like this: If you can’t secure a particular system with the perfect security tool, you compensate by implementing other methods, like tighter access controls, enhanced monitoring, or even manual processes, that help reduce the likelihood of a successful attack.
In a world where online security is constantly evolving and the threat landscape changes by the day, compensating controls offer a realistic, real-world solution. They allow you to maintain a strong security posture without needing to overhaul your entire infrastructure every time a new vulnerability is discovered. They also help meet the expectations of regulatory compliance audits and provide an additional layer of protection.
Why Context Changes Everything
Three layers of compensation matter in any security program.
- At the tool level, overlapping capabilities reinforce each other in incident response and vulnerability management.
- At the controls level, two controls actively support each other’s function.
- At the scenario level, a weak control at one point in the attack chain is backed by a stronger control further along it.
Without visibility across all three layers, your team is reacting to findings that existing controls are already handling. The result is wasted remediation effort, inflated risk scores, and decisions made on incomplete data.
This is where most programs break down. Not because they lack tools. Because those tools are not connected to each other, to the threat picture, or to the business context that determines what actually needs to close.
The Execution Gap Is the Real Problem
Visibility is not the gap. Execution is.
Most security teams already have more data than they act on. Scanners surface findings. Dashboards show exposure. Prioritization engines rank risk. And still, exposure persists. Findings sit in queues. Validation stalls. Remediation depends on senior engineers who are already stretched.
Compensating controls get lost in that noise. They are not reflected in risk scores, not factored into remediation prioritization, and not re-evaluated as assets, threats, and business context change.
The organizations that close exposure fastest treat their security environment as a system, not a collection of dashboards. They correlate assets, vulnerabilities, controls, and threat activity into a single operational view and act on it continuously.
How to Operationalize Compensating Controls
Here’s how to approach it:
- Identify and Document: First, make sure all compensating controls are clearly identified and documented. Whether it’s additional monitoring, multi-factor authentication, or stricter access policies, your team needs to have a clear understanding of each measure taken and controls already in place.
- Evaluate Effectiveness: Assess how well these compensating controls are working. Are they truly mitigating the risk associated with certain exposures, or are they just providing a false sense of security? Regular validation of their effectiveness should be part of your ongoing risk assessments.
- Prioritize Based on Real Risk: Rather than simply reacting to the latest alert or vulnerability, prioritize remediation based on real risk. If compensating controls are effectively addressing a gap, you may be able to delay or even avoid unnecessary remediation, which allows you to focus resources where they’re truly needed.
- Integrate Into Your Workflow: They belong in your risk dashboards, your remediation routing, and your reporting to leadership. Treating them as background context means they will keep getting ignored.
How Nagomi Security Helps Implement Compensating Controls
Nagomi is built on the principle that exposure management is an operational problem, not a visibility problem. The tools exist. The data exists. What is missing is a system that connects them and acts.
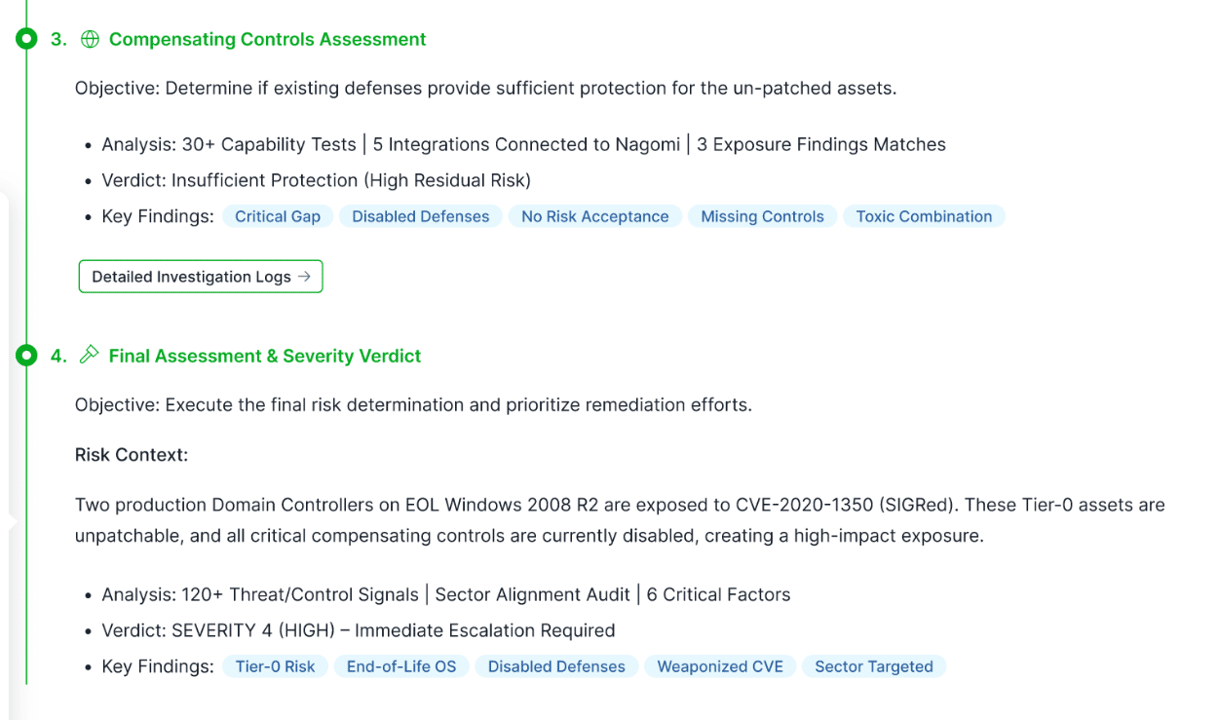
The Nagomi platform correlates assets, vulnerabilities, controls, threat activity, and business context into a continuous operational loop. Compensating controls are a live input into how exposure is evaluated and how remediation is prioritized and executed, not a footnote in a report.
AI agents perform cross-domain validation continuously. They route remediation to the right team. They re-evaluate protection as conditions change. They bring engineers in when judgment or approval is required, not for repetitive validation work.
Your compensating controls are no longer invisible. They are part of a system that acts on real exposure, not theoretical findings.
Where Nagomi Differs From Prioritization-Only Approaches
Some platforms tell you what not to worry about. That is useful. Reducing noise is not the same as closing exposure.
Prioritization tells your team where to look. Nagomi helps you to close what matters and keeps it closed. That is a different operating model. One that reduces dwell time, removes manual handoffs, and gives security leadership verified proof that exposure is shrinking, not just ranked.
The security teams under the most pressure do not need a better dashboard. They need fewer open exposures, a team that is not burned out, and a system that absorbs the complexity of a growing environment without adding headcount to run it.
That is what Nagomi is built to do. Request a demo today.




